The entire population of the world will be connected to the Internet in 2020, said Google boss Eric Schmidt.
“This recent time one third of people online, but the end of this decade every person on Earth will be connected (Internet),” Schmidt was quoted as saying CNET.
According to CNET, the statement was inappropriate because of Schmidt’s most parts of the world is still faced with the question of poverty. and the internet is not a priority.

Google will benefit from the spread of Internet network across the world, especially with the Android and Google Fiber as well as of course the benefit of Google search ads.
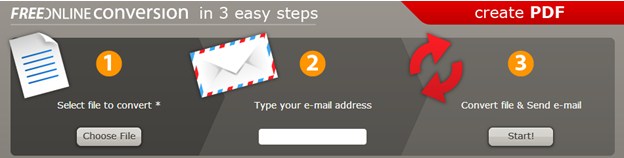
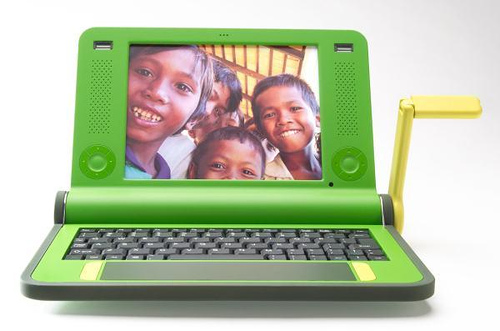
Android technology Media Headlines called Goolge has embarked on a program of GEEKS Without Frontiers.
The goal of creating affordable technology could bring the wireless Internet.
The question that arises from the media and observers of technology in the US that is why Google is so eager to bring Internet and technology support to developing countries? Why Apple doesn’t follow suit?
“This recent time one third of people online, but the end of this decade every person on Earth will be connected (Internet),” Schmidt was quoted as saying CNET.
According to CNET, the statement was inappropriate because of Schmidt’s most parts of the world is still faced with the question of poverty. and the internet is not a priority.

Google will benefit from the spread of Internet network across the world, especially with the Android and Google Fiber as well as of course the benefit of Google search ads.
Android technology Media Headlines called Goolge has embarked on a program of GEEKS Without Frontiers.
The goal of creating affordable technology could bring the wireless Internet.
The question that arises from the media and observers of technology in the US that is why Google is so eager to bring Internet and technology support to developing countries? Why Apple doesn’t follow suit?